Losant Security Overview
The Losant IoT application enablement platform keeps our customers' solutions protected by using the highest level of security. Losant uses industry-standard encryption mechanisms to fully encrypt all data during transit and while at rest. This article provides a detailed overview of how Losant provides a secure environment for its users and applications.
SOC Compliance

Losant is proudly SOC 2 Compliant and undergoes recertification and auditing annually.
SOC Compliance is a set of criteria developed by the American Institute of CPAs (AICPA) that defines how customer data is managed. There are five principles:
- Privacy
- Security
- Confidentiality
- Availability
- Processing Integrity
SOC 2 Compliance, specifically, is a certification given by a third-party auditor that assesses a system's operational effectiveness with those five principles.
Annual Penetration Testing
As part of our SOC compliance, the Losant platform undergoes yearly whitebox penetration testing by an outside firm. A a high level, the firm is tasked with ensuring that:
- One client cannot gain access to another client's data or application configuration.
- One client cannot manipulate another client's telemetry data or application configuration.
- A malicious actor cannot grossly impact the performance, security, or availability of the system architecture.
ISO 27001 Certified

Losant is proud to be ISO 27001 Certified, a process we are audited for and recertified on an annual basis.
ISO certification speaks to our commitment to manage our users' data – as well as their IoT application data – safely and securely.
We regularly audit our internal processes and employee data access to ensure that we follow the guidelines set forth by the ISO standard.
By achieving this certification, Losant's users and customer organizations know that their data is protected from unauthorized access.
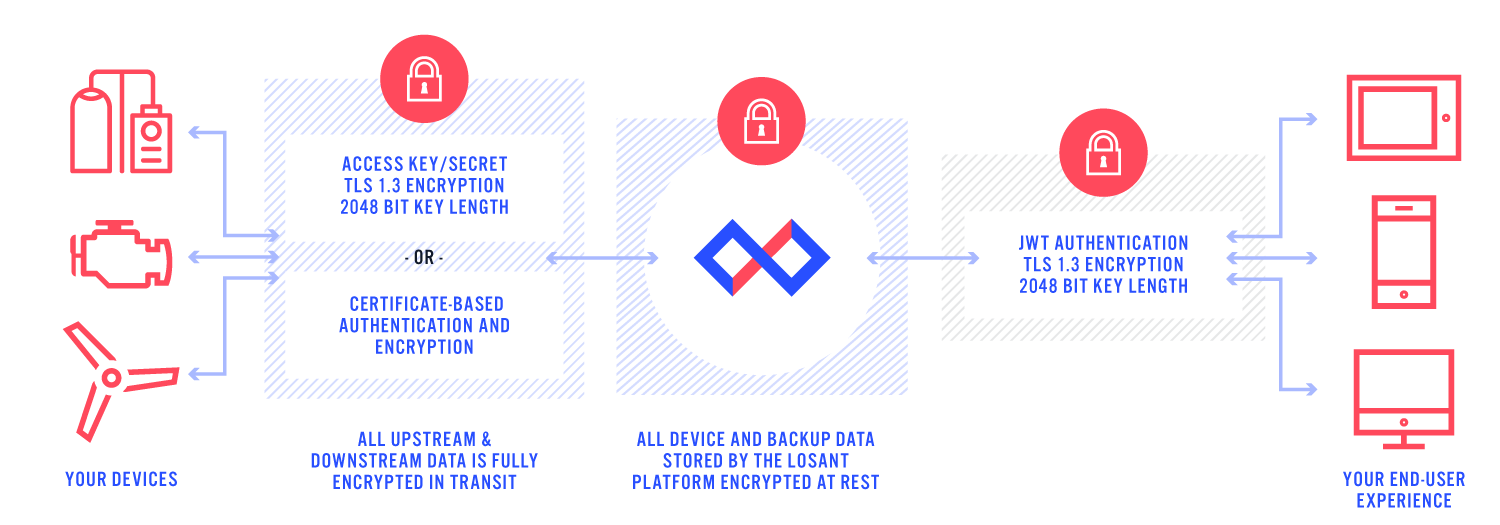
Transport Security
All communication between devices and Losant is fully encrypted using Transport Security Layer (TLS) 1.2 or 1.3. TLS is an industry-standard encryption scheme and most commonly used by browsers to encrypt HTTPS data. TLS is widely adopted and available on most devices, languages, and operating systems.
API Security Tokens
API access is controlled by the industry-standard JSON Web Tokens authentication mechanism. Users create remote API access tokens through the account dashboard. The types of resources available to the token can be individually controlled depending on the needs of the specific API client. For example, an application that only needs access to view data can generate a token that just grants access to data. This token is not be able to view, edit, or manage any information about workflows or devices. API access tokens can be revoked at any time.
Losant does not store the tokens once they are generated; it is up to the user to securely save this information. You cannot recover a token if it is lost. The scope of each token is securely encrypted directly into the token, which is decrypted by Losant server-side. This allows Losant to use the token to grant access to resources without having to store any information about the token directly. The benefit of this approach is that access tokens can never by obtained from any data stored on Losant's servers.
Application Secret and Keys
Devices that communicate using MQTT use application secrets and keys. These are implemented in the same way as API Security Tokens, but automatically scope access to the specific application. The key and secret are used as MQTT's username and password fields respectively.
Infrastructure Security
Losant uses Google Compute as its underlying infrastructure provider. All data is stored using Google Compute Engine's persistent disk functionality, which encrypts all data in transit and at rest. Google complies with the strictest information and physical security requirements. Please refer to their security documentation for more information.
Multi-Factor Authentication
Losant has implemented a multi-factor authentication (MFA) scheme based on the Internet Engineering Task Force standard RFC 6238. The same time-variant-based one-time password algorithm used by Google and Amazon also protects a Losant user's account against unauthorized access even if their password has been compromised.
Was this page helpful?
Still looking for help? You can also search the Losant Forums or submit your question there.